

.svg)
At RapDev, the SOC doesn’t do “same day, different day.” Some days are all about fast triage: working the queue, clearing noise, and making sure real issues don’t get buried. Other days, a single alert becomes a deep dive that turns into a full investigation. On paper, the responsibilities are straightforward: triage incidents, manage alerts, detect threats, and complete post-incident analysis. In practice, it’s a lot more hands-on and collaborative. We partner with cross-functional teams to gather missing context, sanity check what we’re seeing, and confirm escalations with customers. Then we help map out the best fix - because it’s not enough to identify a problem; we need to help get it resolved. The real core of the role, though, is the analysis. Correlating telemetry across identity, infrastructure, and application layers. Looking for the subtle patterns that don’t scream “attack” until you connect the dots. That’s how you catch the sneaky stuff and stay ready for whatever today’s “new baddies” look like in the real world.

Supply chain attacks are no longer edge cases - they’re becoming a routine part of the threat landscape. And more often than not, they don’t start with your environment at all. They start with a trusted third-party vendor. We’ve seen this play out repeatedly in recent high-profile compromises. The npm incident attributed to Shai-Hulud, the Okta vishing attack linked to ShinyHunters, and the Notepad++ compromise tied to Chrysalis all followed a familiar pattern: attackers found a weak link upstream and used that trust to move downstream.
RapDev’s SOC analysts focus their time and expertise by correlating logs across platforms, tracking Cloud SIEM signals, and validating suspicious behavior against known vendor activity; our analysts can separate real risk from background noise. When something doesn’t add up, we dig deeper, conducting targeted security assessments and working with customers to understand potential exposure.
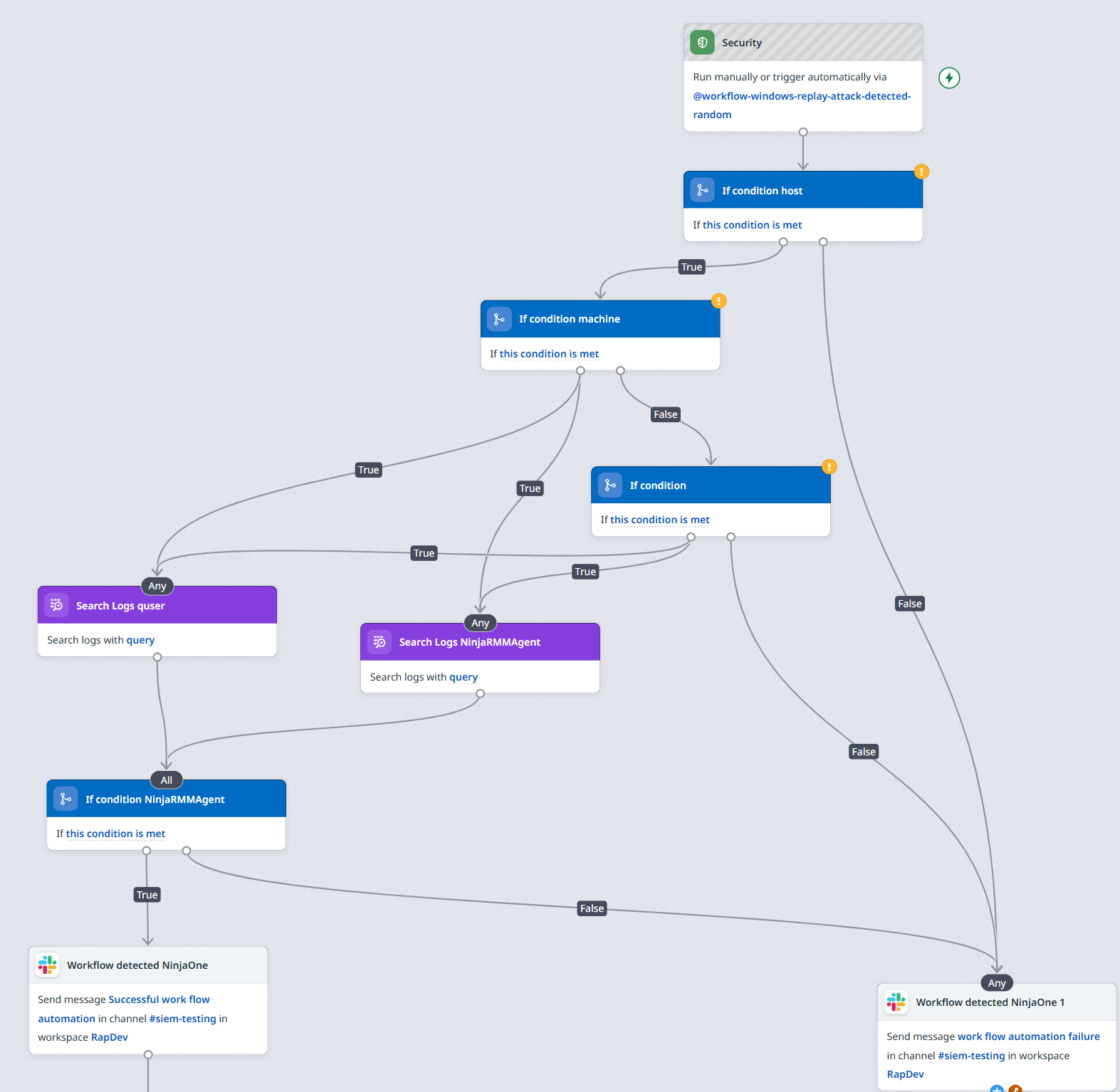
When a security signal fires, the real risk isn’t just the alert itself; it's the context switching that follows. Jumping between tools, rerunning the same searches, and making decisions with partial information adds up fast. That’s where workflows come in. Workflows work best when they’re built from real signals, not assumptions. A handful of representative alerts is usually enough to reveal patterns, clarify what actually matters, and turn a manual assessment process into something efficient and repeatable. A well-designed workflow mirrors how an analyst already thinks, just faster. A typical workflow can include the following steps:
This is where RapDev’s engineering-first approach comes into play. By building structured workflows with a clear purpose, we help analysts stop chasing individual alerts and start making faster, better-informed decisions.
For a RapDev SOC analyst, daily wins rarely come from one big heroic moment. They come from small, incremental improvements—the kind that make tomorrow’s alerts a little easier to handle than today’s. One recent example came from investigating Okta alerts for Impossible Travel and Brute Force activity. At first glance, the signals looked serious. But instead of jumping between multiple log searches to piece together what was happening, we leaned into Datadog Log Search Views.
By pulling user IDs, event names, location data (cities and countries), and event outcomes into a single view, the picture got a lot clearer fast. What normally would have required several separate queries turned into one focused investigation. That clarity paid off. After correlating the events, we realized the alerts weren’t pointing to a real attack at all. A recent update, combined with an ad-sync issue, was generating the same behavior across multiple users, triggering false positives. Once identified, we were able to tune the signals and reduce unnecessary noise going forward. It wasn’t a dramatic save, but it was a real win. Fewer false positives, faster investigations, and more time spent on threats that actually matter.
This is what RapDev’s Managed SOC delivers every day: experienced analysts, smarter workflows, and continuous improvement driven by real-world signals. We don’t just respond to alerts, we reduce noise, accelerate investigations, and help teams stay ahead of evolving threats with clarity and confidence.
If your security team is buried in alerts, struggling with signal quality, or looking to get more out of Datadog Security, we can help. Contact us to learn more about RapDev’s Managed SOC services and how we turn security operations into an engineering discipline.
We go further and faster when we collaborate. Geek out with our team of engineers on our learnings, insights, and best practices to unlock maximum value and begin your business transformation today.
How financial services firms use Datadog to modernize monitoring while meeting strict regulatory demands

Healthcare orgs risk sensitive data by relying on legacy tech and lacking modern observability
