Why Code Security Matters
Code security is vital to a true DevSecOps approach. Leveraging a variety of tools allows organizations to establish a “security first” approach to building, maintaining, and deploying software and services in their environments. While tackling code security can initially be a daunting task, the sooner it is integrated into an organization’s lifecycle, the sooner it can reap the benefits.
Overview
- Software Composition Analysis (SCA)
SCA can be used by DevSecOps teams to maintain visibility in the open source packages and their licenses used in code development. As new vulnerabilities are constantly discovered, Software Composition Analysis (SCA) provides ongoing vulnerability detection and monitoring for DevSecOps organizations, allowing them to swiftly remediate issues and reduce their attack surface. - Static Application Security Testing (SAST)
SAST analyzes source code for projects without executing the project. Static Application Security Testing (SAST) enables developers to fix flaws earlier, reducing time spent down the line to remediate security issues. Utilizing SAST tools also enables better code quality, allowing developers to create readable and maintainable code that can be easily used and updated. - Interactive Application Security Testing (IAST)
AST is commonly used by DevSecOps teams in place of Dynamic Application Security Testing (DAST). IAST solutions are newer tools that perform a combination of static and runtime analysis. These tools are made to be used for continuous monitoring, with agents baked into software so that developers get real-time vulnerability reports. By utilizing a combination of IAST and SAST, DevSecOps teams have continuous monitoring of their software and services, with SAST providing additional tooling in the areas that IAST does not yet support.
The Implementation
Implementing code security can be really overwhelming - how do you decide where to start? Lucky for you, Datadog makes this easy. DevSecOps teams can integrate a wide range of tools into their development environments, including, but not limited to SCA, SAST, and IAST tools.
- Enabling Code Scanning
Datadog allows teams to quickly and easily add these tools to their environments. To enable static scanning in repositories, simply select your source code management environment (like GitHub or Azure DevOps), select where the scans should be run (either in Datadog itself or your pipeline), connect your account, and then enable scanning. When enabling static scanning like SAST or SCA, you can opt to enable it throughout your repositories or select repositories individually that you want to scan. IAST is enabled a bit differently, where you select the language used in your repository, update the agent used for the language, and then run the application or container it’s hosted in with a parameter used to enable IAST scanning by Datadog. Following this, restarting the service and generating live traffic will begin the active IAST scanning, with results appearing shortly after in your Datadog instance. - Quality Gates and PR Gates
Similarly, there are ways to use the information these tools provide to block pull requests with bad code from being pushed to production. Implementing these controls, organizations can prevent code without unit tests, code where the quality falls below certain standards, or code with critical or high vulnerabilities from being pushed to production environments. With Datadog’s Quality and PR gates, teams can now easily perform this type of active prevention.
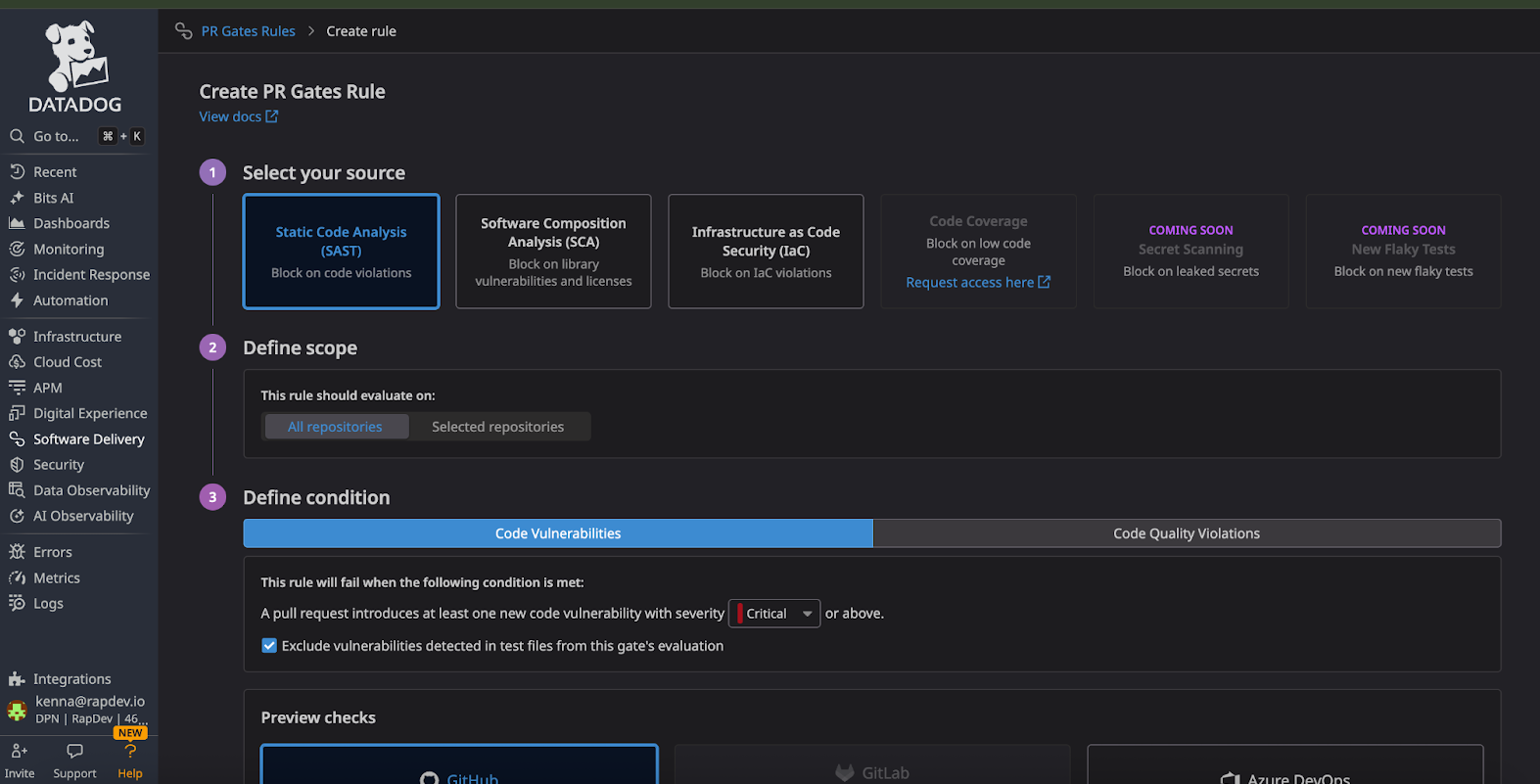
With Quality gates, you can select the rule type, scope, and rule condition. You then name the rule and add it to your code pipeline. Teams can also enable previews of the checks to display in their active PRs by marking the check as required in their projects, allowing them to see before their code runs through the pipeline if they are passing or failing checks. Creating PR gates is a similar process, where you select your source, what repositories you want this applied to, and the rule condition. These features allow teams to block pull requests with failing tests, vulnerabilities, best practice violations, or licensing issues before they can enter their production environments, reducing the likelihood of an exploitable vulnerability making it all the way through the deployment process.
Why Datadog for Code Security
Aside from social engineering tactics, one of the most common attack vectors is exploiting vulnerable software and services - adding code security to your environment will only reduce your attack surface and remediation costs. Datadog can not only provide these tools, but also give teams the insight and ability to quickly remediate any issues found.
While Datadog is usually not at the forefront of someone’s mind when they think of code security, the variety of tools in the platform provides a holistic and in-depth view of the problems present in a development environment. If you or your team want to know more or need help getting set up with Datadog Security, contact us.







