How to Actually Mature Your Threat Hunting Program on Datadog
Most threat hunting programs don't fail because of a lack of talent. They stall because no one mapped out what "better" actually looks like in practice. This post sets out to identify that — stage by stage, with specific actions tied to Datadog capabilities. I aim to give you a way of assessing where you are today and get an idea of some paths forward. Emphasis on “some!”
Level 0 → Level 1: Stop Reacting, Start Ingesting
At Level 0, everything is reactive. Detections fire, analysts triage, life moves on. Log ingestion is scoped to the bare minimum. The observability side of Datadog like metrics and traces might as well not exist from a security standpoint.
The problem here is threefold: not enough data, no structure, and limited platform depth. Fixing it requires attacking all three at once.
What to do:
- Audit your current log sources. Categorize each by volume, threat protection value, and hunting value. Use that taxonomy to justify broader ingest — particularly sources you've been excluding for cost or convenience reasons.
- Begin CTI ingest. Even an RSS feed into Slack is a starting point. The goal is to replace ad-hoc research with a repeatable information pipeline.
- Assign at least one analyst explicit, protected time for proactive searching — distinct from their triage queue. You can't build a hunt program in the margins of an alert-driven workday.
- Get your security team trained on Datadog's full platform, not just the Security tabs. Log Explorer query syntax, saved views, visualization techniques, and time-range analysis should be baseline competencies.
Level 1 → Level 2: Build the Process, Not Just the Capability
At Level 1, things are improving — broader log access, some CTI integration, analysts occasionally pivoting into the observability layer. But hunts are still ad hoc. If your lead analyst left tomorrow, the program would lose half its institutional knowledge.
The core problems at this stage are data scale and lack of structure. You have more data than you know what to do with, and no systematic way of using it.
What to do:
- Establish a hunting schedule. Hunts need to be a recurring operational commitment, not something that happens when there's extra time.
- Build out your threat model. It should be specific enough to generate hunting targets, not just a list of generic MITRE techniques. What does your actual environment look like? Who wants into it, and how?
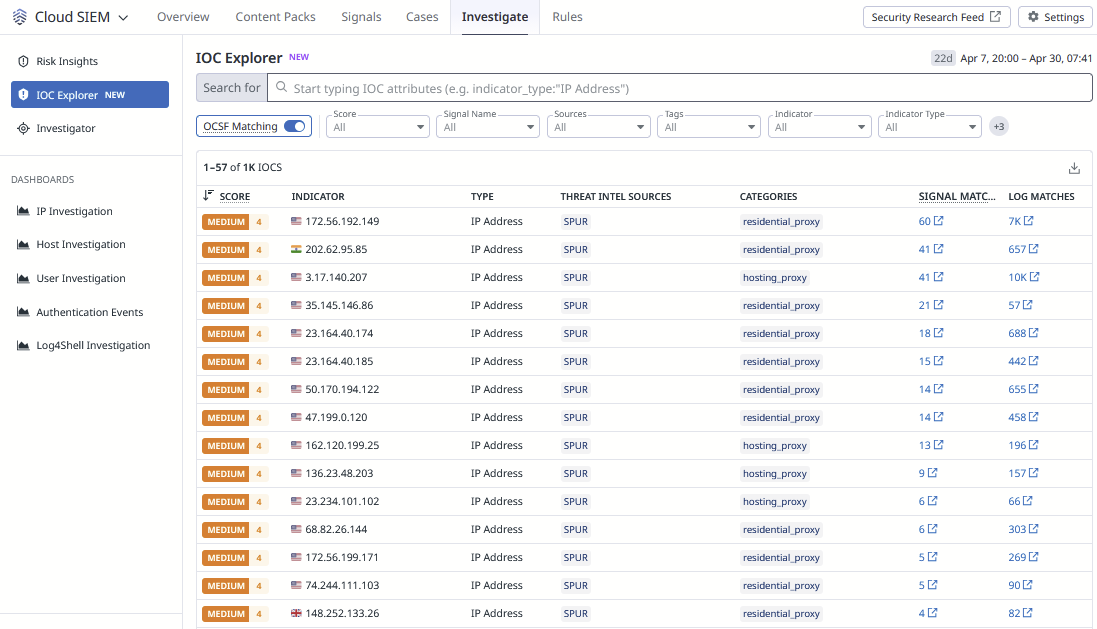
- Operationalize the IOC Explorer — use it for frequency and pattern analyses, not just lookups. Load custom threat intelligence into Datadog via the Bring-Your-Own-Threat-Intelligence feature and keep it updated.
- Train security personnel specifically on observability features — metrics, traces, service maps — and begin incorporating that data into security context. Analysts should be able to pivot between Security and Observability fluidly.
- Write down everything. SOPs, hunt playbooks, program ownership. If the knowledge only lives in someone's head, you don't have a Level 2 program — you have a person.
Level 2 → Level 3: Go From Consumers to Producers
A Level 2 team runs good hunts on a schedule, uses solid threat intelligence, and understands their environment. The ceiling here is creativity and scale. You're executing repeatable processes, but you're not yet producing new ones. Teams at this level are (or should be) also looking at incorporating scaling automation and AI use cases.
What to do:
- Promote or hire dedicated threat hunters. This is the non-negotiable Level 3 gate. Analysts with a side-hunting responsibility are not threat hunters. The job needs to be the job.
- Start leveraging Historical Searches systematically — apply new threat intelligence retroactively across your log corpus to identify detections you should have built earlier and patterns that warrant deeper investigation.
- Customize Workflow Automation Blueprints for hunt support. Don't just run the OOTB blueprints — build and modify them to automate data gathering and analysis tasks that currently eat analyst time.
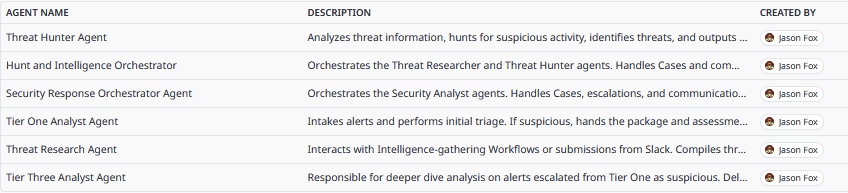
- Begin experimenting with Agent Builder's Cybersecurity Responder Agent. At this stage, minimal configuration gets you meaningful augmentation on investigation tasks. Let the agent handle lower-complexity legwork while hunters focus on analysis.
Level 3 → Level 4: Automate What You've Proven, Invent What Doesn't Exist Yet
At Level 4, the program is institutionally resilient — it doesn't depend on any individual, leadership transitions are documented, and automation handles a meaningful portion of lower-sophistication hunting operations. The creative challenge at this stage is pushing into territory that hasn't been mapped yet.
What to do:
- Build custom Agents with bespoke instructions, purpose-built for your environment and threat model. The generic Cybersecurity Responder is a starting point, not a destination.
- Develop Workflow Automations capable of fully executing lower-sophistication hunts end-to-end — not just supporting them.
- Push hunting into non-traditional telemetry. Can your team hunt through metrics and traces with the same fluency they bring to logs? Can you extract adversary signals from cloud cost anomalies or service latency patterns? That's the frontier.
- Revisit and update all SOPs and playbooks regularly. A Level 4 program doesn't just survive personnel changes — it thrives through them because the knowledge is embedded in the process.
The Honest Assessment
Maturity is not a destination you arrive at, it's a current state you're always moving away from. The teams that do this well aren't the ones with the biggest budgets. They're the ones who know where they are, know what the next stage looks like, and execute against it deliberately.
If you're not sure which level your program sits at, then contact us! RapDev lives and breathes Datadog and security. And we don’t just claim that – we have years of experience working with organizations around the world, big and little, new to Datadog and not. RapDev has an answer to any problem you have, so let’s build something better together! If you need Datadog implementation assistance, need to optimize your spend, or need a trusted security partner, contact us today!





.svg)

